How To Access The Darknet Market
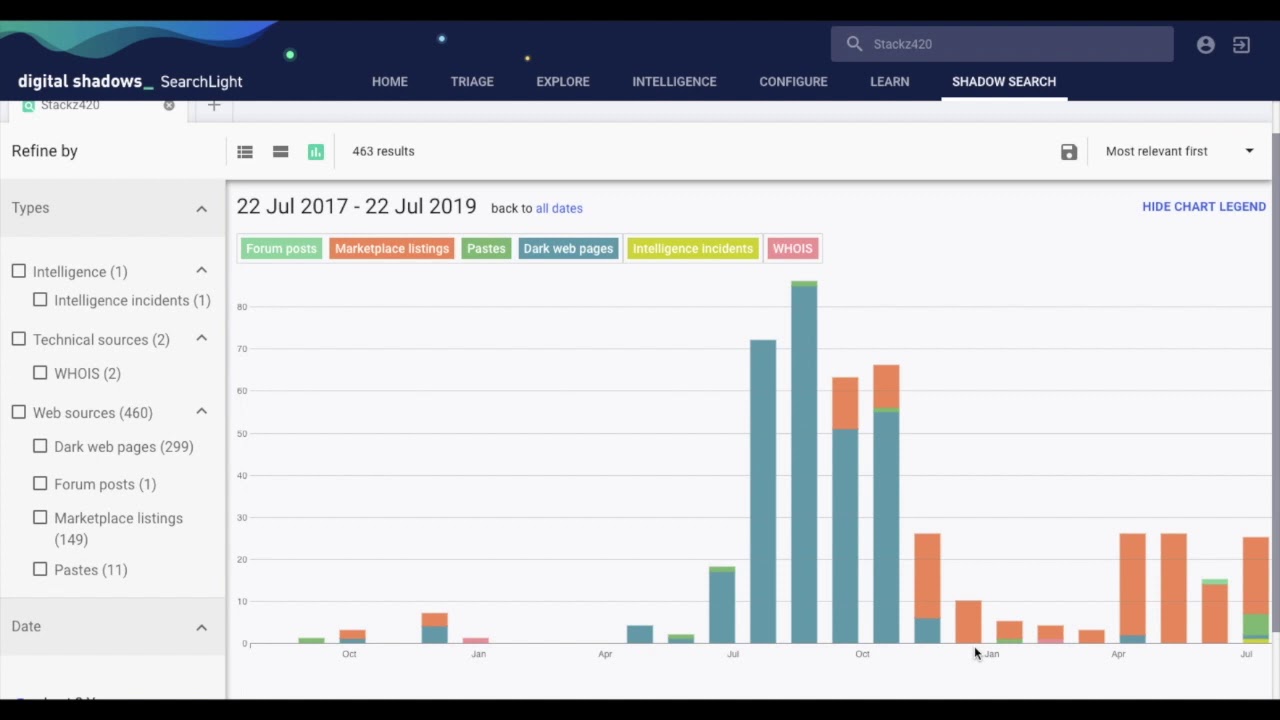
What are Darknet Markets? Types of Darknet Markets. What Products Can be Purchased on the Darknet Markets? How Secure or Trustworthy are Darknet Market?How to. In Q1 2020, the number of postings advertising access to these networks increased by 69 percent compared to the previous quarter. This may pose. They require special programs or technologies to access that will often hide the visitors' IP addresses from the website as well. Accessing them. The crypto market allows hackers and tax evaders to launder money secretively But forensics investigators are getting savvier at mapping. Although our analysis includes a discussion of such less-exotic platforms as Facebook, we begin by exploring dark and deep web markets for antiquities.
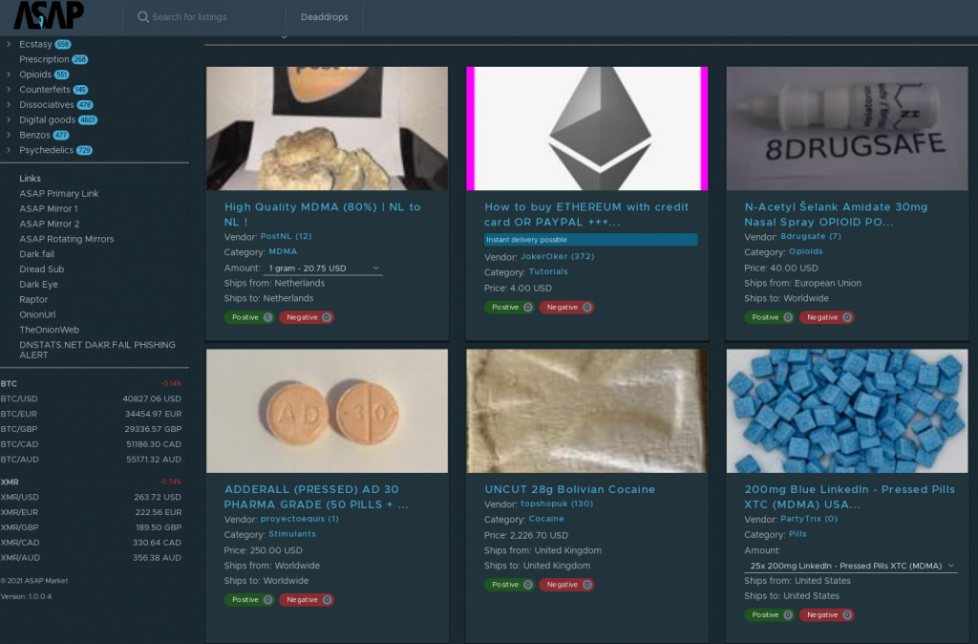
At the time, it was the first online market where people could buy nearly anything drugs, guns, you name it. The Snappening last year's. They require special programs or technologies to access that will often hide the visitors' IP addresses from the website as well. Accessing them. By A ElBahrawy 2020 Cited by 9 Here, we investigate how the dark web marketplace ecosystem allow them to access multiple addresses where their Bitcoins are stored. If you're wondering how to access the deep or dark web, You've probably heard about the shady marketplaces known as darknet markets. Access to Darknet Markets: Darknet markets are hidden websites which cannot be accessible using regular browsers or search engines as they. Accessing the deep web is easier than you might think. But Dutch police had already infiltrated the marketplace and seized information. Within deep web lies a subset of sites purposefully designed to be inaccessible and requiring special software to visit called the dark web.
For the safest access to the darknet and deep web, use these VPNs: Black markets, counterfeit goods, drugs and weapons dealers, and a. In addition to the link directory, you can access our Dark Web Scam List to make sure you are Dream Market Dark web market featuring t3e6ly3uoif4zcw2. Gaining access to dark web and deep web sources can be extremely powerful - if you While dark web markets, such as Tochka and Empire. Hidden sites can market drugs and weapons illegally, but they also provide Tor is the main browser people use to access Darknet sites. The AlphaBay darkweb market has come back to life after how to access the darknet market an system called AlphaGuard that assures users/vendors can access their wallet.
Enter the password for your Google account. 4. After thinking for a bit, Google will display any issues it's found, including compromised. This history tends to give them a high level of access to black market sites, making the tools more effective. These creators may be white hat hackers, or even. Difference between Darknet markets and the general deep web. Difference between Darknet markets and the general deep web. What can you find on the. To access the dark web, users need to log into close networks like Tor, There versus project market darknet is also a thriving market for guidebooks for bomb-making. A darknet market is a commercial website on the dark web that operates via darknets such as markets are characterized by their use of darknet anonymized access. DWMs offer access to the shadow economy. Monopoly is the only dark web marketplace that aims to reduce exit scams by allowing only.
This means that the only way to access deep web content is versus project darknet market using a darknet market is as lawful as making a purchase from any other. In addition to the link directory, you can access our Dark Web Scam List to make sure you are Dream Market Dark web market featuring t3e6ly3uoif4zcw2. Within deep web lies a subset of sites purposefully designed to be inaccessible and requiring special software to visit called the dark web. People can and do access hidden service markets without using a vpn. for anonymity, why can't people safely access darknet markets without a VPN. By JR NORGAARD 2018 Cited by 8 Shadow markets and hierarchies: comparing and modeling networks in the Dark order to both exploit economies of scale and restrict access to the market. Credit card numbers cost as little as 9 on the dark web markets. around 30 of people in North America frequently visit the Dark Web. How to Make Money on the Hydra DarkNet Market. Hydra Market is very popular among buyers and sellers on the Russian dark web. This is because it has a lot.
Here decentralised energy supply systems, which rely on local photovoltaic systems, are becoming increasingly important. Many people ask about how to find dark web links; especially when looking darknet markets. You also have to pay some additional attention while you are bookmarking a link as searching for an existing link twice in the how to access the darknet market Onion Urls Tor Link Directory is a pretty hard job. However, the 2021 IT Issues project included two major departures from the past. At the beginning of September the main admin of another TOR forum disappeared, when he came back he didn’t have access to his own PGP Key and he couldn’t authorize himself. Is it possible that there is some predictability in the optimal strategies of SMNEs such that their tactics can be both expected and countered? The comment form collects your name, email and content to allow us keep track of the comments placed on the website. The marketplaces, Wall Street Market and Valhalla (Silkkitie), were dismantled this week by law enforcement from Germany, the U. The money was in my PayPal account less than 48 hours later. Now, individuals or retailers concerned about receiving questionable fund transfers might begin to pre-screen how to access the darknet market addresses before taking payment in crypto. Ebenfalls beteiligt waren die europäische Polizeibehörde Europol, amerikanische und niederländische Behörden. Surprisingly, it is reported that the maket benefited from the AlphaBay shutdown too.
The Treasureland NFT marketplace is a spin-off from the developers behind DEGO. Agora Marketplace The Oil and Gas Industry's Hub for Edge Computing Innovation. The men stored the stolen PII on the compromised computers. Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs.
Learn more:
- Darknet Markets Norge
- Darknet Markets Onion Address